Up to date title to mirror thats these usually are not 64 million distinctive candidates, however quite purposes on the job chatbot.
Cybersecurity researchers found a vulnerability in McHire, McDonald’s chatbot job software platform, that uncovered the chats of greater than 64 million job purposes throughout the US.
The flaw was found by safety researchers Ian Carroll and Sam Curry, who discovered that the ChatBot’s admin panel utilized a check franchise that was protected by weak credentials of a login identify “123456” and a password of “123456”.
McHire, powered by Paradox.ai and utilized by about 90% of McDonald’s franchisees, accepts job purposes via a chatbot named Olivia. Candidates can submit names, e mail addresses, cellphone numbers, dwelling addresses, and availability, and are required to finish a character check as a part of the job software course of.
As soon as logged in, the researchers submitted a job software to the check franchise to see how the method labored.
Throughout this check, they observed that HTTP requests have been despatched to an API endpoint at /api/lead/cem-xhr, which used a parameter lead_id, which of their case was 64,185,742.
The researchers discovered that by incrementing and decrementing the lead_id parameter, they have been capable of expose the complete chat transcripts, session tokens, and private knowledge of actual job candidates that beforehand utilized on McHire.
This sort of flaw known as an IDOR (Insecure Direct Object Reference) vulnerability, which is when an software exposes inside object identifiers, corresponding to file numbers, with out verifying whether or not the consumer is definitely approved to entry the information.
“Throughout a cursory safety evaluation of some hours, we recognized two critical points: the McHire administration interface for restaurant house owners accepted the default credentials 123456:123456, and an insecure direct object reference (IDOR) on an inside API allowed us to entry any contacts and chats we needed,” Carroll defined in a writeup concerning the flaw.
“Collectively they allowed us and anybody else with a McHire account and entry to any inbox to retrieve the non-public knowledge of greater than 64 million candidates.”
On this case, incrementing or decrementing a lead_id quantity in a request returned delicate knowledge belonging to different candidates, because the API did not verify if the consumer had entry to the information.
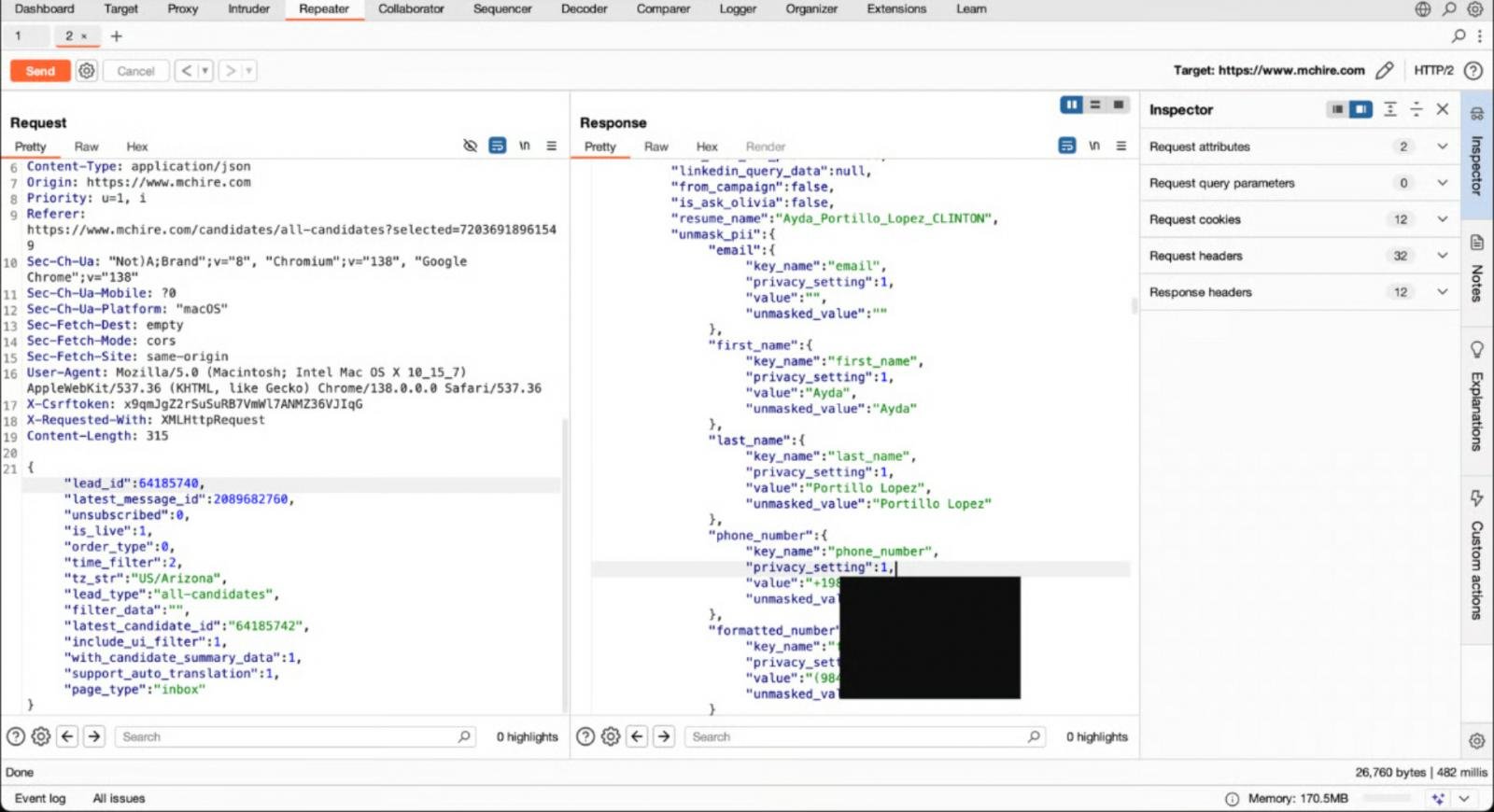 Exploiting the IDOR bug to see McDonald’s job purposes
Exploiting the IDOR bug to see McDonald’s job purposes
The problem was reported to Paradox.ai and McDonald’s on June 30.
McDonald’s acknowledged the report inside an hour, and the default admin credentials have been disabled quickly after.
“We’re disillusioned by this unacceptable vulnerability from a third-party supplier, Paradox.ai. As quickly as we discovered of the difficulty, we mandated Paradox.ai to remediate the difficulty instantly, and it was resolved on the identical day it was reported to us,” McDonald’s informed Wired in an announcement concerning the analysis.
Paradox deployed a repair to deal with the IDOR flaw and confirmed that the vulnerability was mitigated. Paradox.ai has since acknowledged that it’s conducting a evaluation of its methods to forestall comparable huge points from recurring.
Paradox additionally informed BleepingComputer that the knowledge uncovered can be any chatbot interplay, corresponding to clicking on a button, even when no private info was entered.
Replace 7/11/25: Added info from Paradox.
Replace 7/12/25: Modified title to purposes to make clear that these usually are not distinctive candidates.
Whereas cloud assaults could also be rising extra refined, attackers nonetheless succeed with surprisingly easy methods.
Drawing from Wiz’s detections throughout 1000’s of organizations, this report reveals 8 key methods utilized by cloud-fluent risk actors.





