Right this moment we’re excited to announce OSS Rebuild, a brand new challenge to strengthen belief in open supply bundle ecosystems by reproducing upstream artifacts. As provide chain assaults proceed to focus on widely-used dependencies, OSS Rebuild provides safety groups highly effective information to keep away from compromise with out burden on upstream maintainers.
The challenge includes:
Automation to derive declarative construct definitions for current PyPI (Python), npm (JS/TS), and Crates.io (Rust) packages.
SLSA Provenance for 1000’s of packages throughout our supported ecosystems, assembly SLSA Construct Degree 3 necessities with no writer intervention.
Construct observability and verification instruments that safety groups can combine into their current vulnerability administration workflows.
Infrastructure definitions to permit organizations to simply run their very own situations of OSS Rebuild to rebuild, generate, signal, and distribute provenance.
Challenges
Open supply software program has develop into the inspiration of our digital world. From vital infrastructure to on a regular basis purposes, OSS elements now account for 77% of recent purposes. With an estimated worth exceeding $12 trillionopen supply software program has by no means been extra integral to the worldwide financial system.
But this very ubiquity makes open supply a horny goal: Latest high-profile provide chain assaults have demonstrated refined strategies for compromising widely-used packages. Every incident erodes belief in open ecosystems, creating hesitation amongst each contributors and shoppers.
The safety neighborhood has responded with initiatives like Safety Scorecard, pypi’s Trusted Publishersand npm’s native SLSA help. Nevertheless, there isn’t a panacea: Every effort targets a sure facet of the issue, usually making tradeoffs like shifting work onto publishers and maintainers.
Our Intention
Our goal with OSS Rebuild is to empower the safety neighborhood to deeply perceive and management their provide chains by making bundle consumption as clear as utilizing a supply repository. Our rebuild platform unlocks this transparency by using a declarative construct course of, construct instrumentation, and community monitoring capabilities which, throughout the SLSA Construct framework, produces fine-grained, sturdy, reliable safety metadata.
Constructing on the hosted infrastructure mannequin that we pioneered with OSS Fuzz for reminiscence concern detection, OSS Rebuild equally seeks to make use of hosted sources to deal with safety challenges in open supply, this time aimed toward securing the software program provide chain.
Our imaginative and prescient extends past any single ecosystem: We’re dedicated to bringing provide chain transparency and safety to all open supply software program improvement. Our preliminary help for the PyPI (Python), npm (JS/TS), and Crates.io (Rust) bundle registries—offering rebuild provenance for a lot of of their hottest packages—is just the start of our journey.
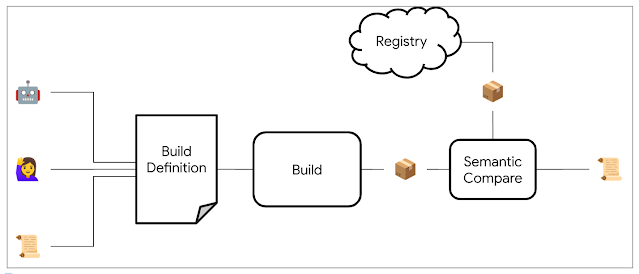
By means of automation and heuristics, we decide a potential construct definition for a goal bundle and rebuild it. We semantically evaluate the outcome with the prevailing upstream artifact, normalizing every one to take away instabilities that trigger bit-for-bit comparisons to fail (e.g. archive compression). As soon as we reproduce the bundle, we publish the construct definition and consequence by way of SLSA Provenance. This attestation permits shoppers to reliably confirm a bundle’s origin throughout the supply historical past, perceive and repeat its construct course of, and customise the construct from a known-functional baseline (or perhaps even use it to generate extra detailed Sboms).
With OSS Rebuild’s current automation for PyPI, npm, and Crates.io, most packages acquire safety effortlessly with out consumer or maintainer intervention. The place automation is not at the moment capable of totally reproduce the bundle, we provide handbook construct specification so the entire neighborhood advantages from particular person contributions.
And we’re additionally excited on the potential for AI to assist reproduce packages: Construct and launch processes are sometimes described in pure language documentation which, whereas troublesome to make the most of with discrete logic, is more and more helpful to language fashions. Our preliminary experiments have demonstrated the strategy’s viability in automating exploration and testing, with restricted human intervention, even in essentially the most complicated builds.
Our Capabilities
OSS Rebuild helps detect a number of lessons of provide chain compromise:
Unsubmitted Supply Code – When revealed packages comprise code not current within the public supply repository, OSS Rebuild won’t attest to the artifact.
Construct Setting Compromise – By creating standardized, minimal construct environments with complete monitoring, OSS Rebuild can detect suspicious construct exercise or keep away from publicity to compromised elements altogether.
Stealthy Backdoors – Even refined backdoors like xz usually exhibit anomalous behavioral patterns throughout builds. OSS Rebuild’s dynamic evaluation capabilities can detect uncommon execution paths or suspicious operations which might be in any other case impractical to determine by handbook evaluate.
For enterprises and safety professionals, OSS Rebuild can…
Improve metadata with out altering registries by enriching information for upstream packages. No want to keep up customized registries or migrate to a brand new bundle ecosystem.
Increase SBOMs by including detailed construct observability data to current Software program Payments of Supplies, making a extra full safety image.
Speed up vulnerability response by offering a path to vendor, patch, and re-host upstream packages utilizing our verifiable construct definitions.
For publishers and maintainers of open supply packages, OSS Rebuild can…
Strengthen bundle belief by offering shoppers with unbiased verification of the packages’ construct integrity, whatever the sophistication of the unique construct.
Retrofit historic packages’ integrity with high-quality construct attestations, no matter whether or not construct attestations have been current or supported on the time of publication.
Cut back CI security-sensitivity permitting publishers to give attention to core improvement work. CI platforms are likely to have complicated authorization and execution fashions and by performing separate rebuilds, the CI surroundings now not must be load-bearing to your packages’ safety.
Test it out!
The best (however not solely!) method to entry OSS Rebuild attestations is to make use of the offered Go-based command-line interface. It may be compiled and put in simply:
$ go set up github.com/google/oss-rebuild/v0/cmd/oss-rebuild
You possibly can fetch OSS Rebuild’s SLSA Provenance:
$ oss-rebuild get cratesio syn 2.0.39
..or discover the rebuilt variations of a specific bundle:
$ oss-rebuild checklist pypi absl-py
..and even rebuild the bundle for your self:
$ oss-rebuild get npm lodash 4.17.20 –format=dockerfile |
docker run $(docker buildx construct -q -)
Be part of Us in Serving to Safe Open Supply
OSS Rebuild isn’t just about fixing issues; it is about empowering end-users to make open supply ecosystems safer and clear by collective motion. In case you’re a developer, enterprise, or safety researcher desirous about OSS safety, we invite you to comply with alongside and become involved!




I love how you write—it’s like having a conversation with a good friend. Can’t wait to read more!This post pulled me in from the very first sentence. You have such a unique voice!Seriously, every time I think I’ll just skim through, I end up reading every word. Keep it up!Your posts always leave me thinking… and wanting more. This one was no exception!Such a smooth and engaging read—your writing flows effortlessly. Big fan here!Every time I read your work, I feel like I’m right there with you. Beautifully written!You have a real talent for storytelling. I couldn’t stop reading once I started.The way you express your thoughts is so natural and compelling. I’ll definitely be back for more!Wow—your writing is so vivid and alive. It’s hard not to get hooked!You really know how to connect with your readers. Your words resonate long after I finish reading.