AsyncRAT has cemented its place as a cornerstone of recent malware and as a pervasive menace that has advanced right into a sprawling community of forks and variants. Whereas its capabilities aren’t that spectacular on their very own, it’s the open-source nature of AsyncRAT that has actually amplified its affect. This blogpost gives an outline and evaluation of probably the most related forks of AsyncRAT, drawing connections between them and exhibiting how they’ve advanced.
Key factors of this blogpost:
We offer distinctive insights into the panorama of AsyncRAT and its quite a few variants to be able to navigate the labyrinth of forks simply.
Within the effort to map the huge hierarchy of AsyncRAT’s forks, we uncover their distinctive interconnections and doc how these variants could be distinguished.
We discover much less frequent variants that function distinctive plugins, starting from a fundamental screamer plugin to a USB malware spreader.
Origins of AsyncRAT
You might have heard of AsyncRAT, brief for asynchronous distant entry trojan. This open-source RAT was launched on GitHub in 2019 by a consumer going by the identify of NYAN CAT. Developed in C#, it affords a variety of typical RAT functionalities, together with keylogging, display capturing, credential theft, and extra. Its simplicity and open-source nature has made it a well-liked selection amongst cybercriminals, resulting in its widespread use in varied cyberattacks.
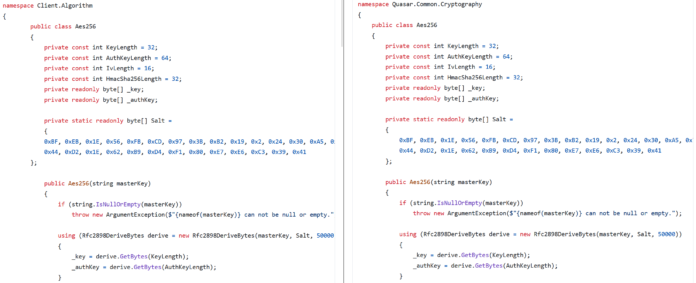
However the place does it come from? We consider that the groundwork for AsyncRAT was laid earlier by the Quasar RAT, which has been out there on GitHub since 2015 and includes a related strategy. Each are written in C#; nonetheless, their codebases differ essentially, suggesting that AsyncRAT was not only a mere fork of Quasar, however an entire rewrite. A fork, on this context, is a private copy of another person’s repository that one can freely modify with out affecting the unique undertaking. The principle hyperlink that ties them collectively lies within the customized cryptography courses used to decrypt the malware configuration settings. Particularly, these are courses Aes256 and Sha256, which fall below the Consumer.Algorithm namespace for AsyncRAT and the Quasar.Frequent.Cryptography namespace for Quasar. Determine 1 reveals equivalent code being utilized in each implementations of Aes256.
Determine 1. Comparability of cryptography courses between AsyncRAT (left) and Quasar (proper)
The identical code is generally copied and pasted, together with the identical salt worth and decryption settings. This class, along with Sha256, leads us to consider that AsyncRAT was to a point influenced by the Quasar RAT.
Aside from these similarities, AsyncRAT launched vital enhancements, notably in its modular structure and enhanced stealth options, which make it extra adaptable and tougher to detect in trendy menace environments. Its plugin-based structure and ease of modification have sparked the proliferation of many forks, pushing the boundaries even additional.
Fork labyrinth
Ever because it was launched to the general public, AsyncRAT has spawned a large number of latest forks which have constructed upon its basis. A few of these new variations have expanded on the unique framework, incorporating extra options and enhancements, whereas others are basically the identical model in several garments.
Fork hierarchy
Determine 2 illustrates how among the extra prevalent AsyncRAT forks have advanced from each other over time.
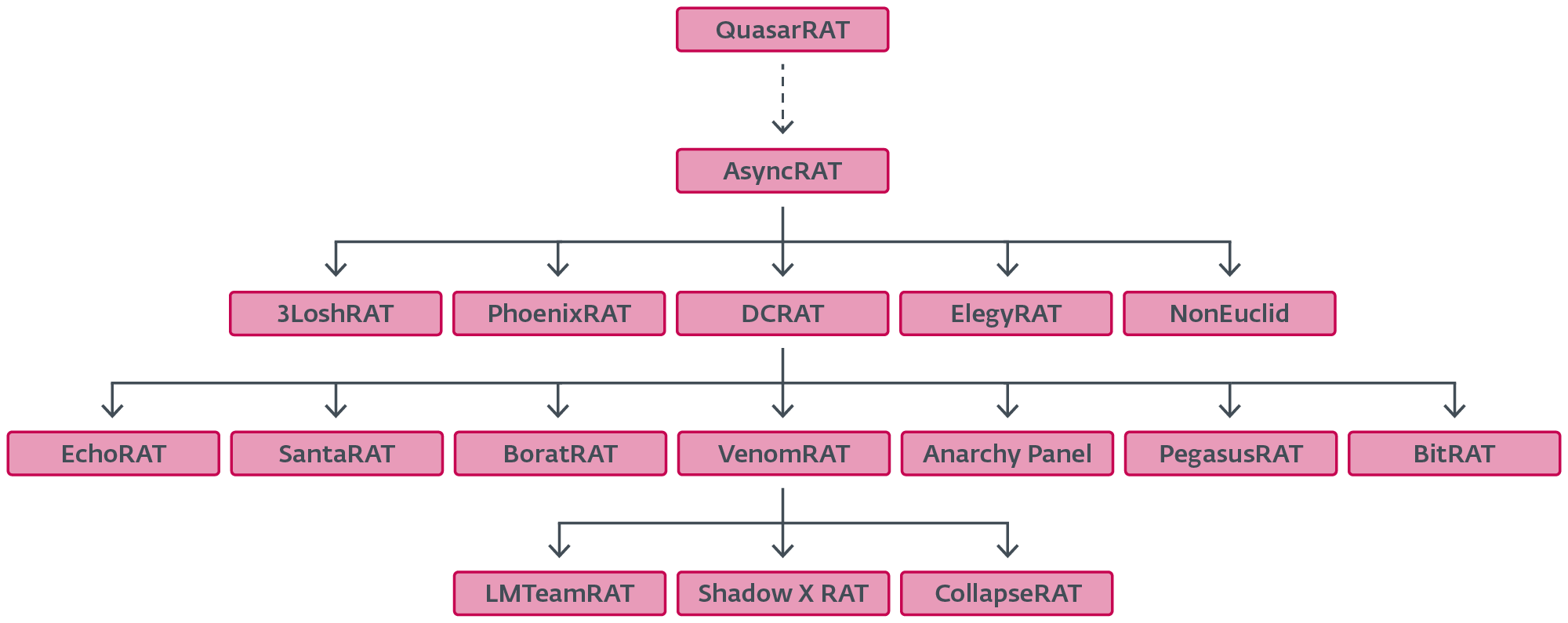
Determine 2. A small subset of forks highlighting their spinoff relationships
In the course of the tree are DcRat and VenomRAT. Our evaluation has proven that they’re probably the most extensively deployed variants, collectively accounting for a big variety of campaigns. Different lesser-known forks occupy smaller however nonetheless notable parts of the pie. Determine 3 depicts the distribution of probably the most prevalent forks in response to our telemetry.
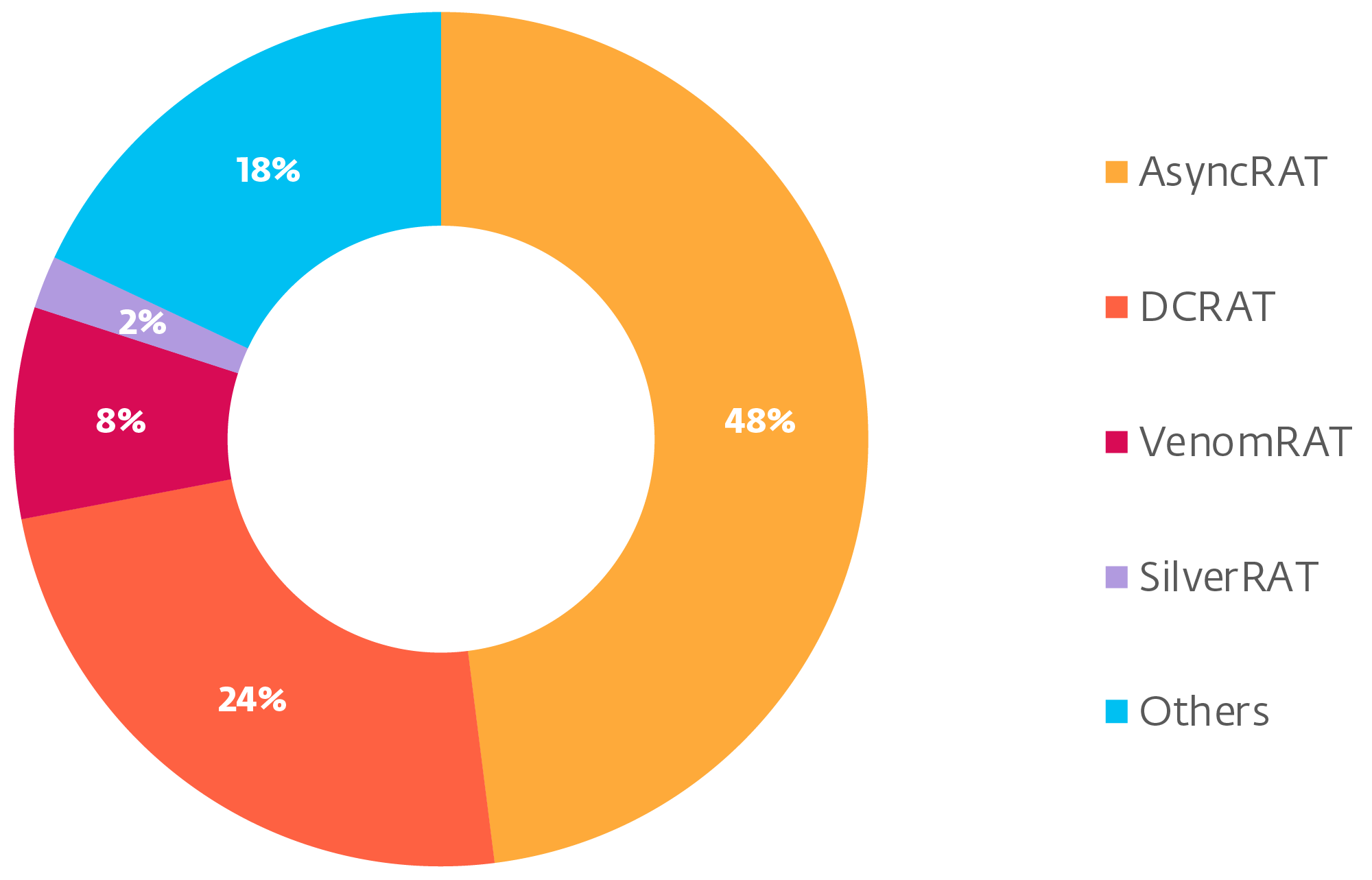
Determine 3. Q2 2024 distribution of the most typical forks, as measured by the variety of distinctive samples
DcRat affords a notable enchancment over AsyncRAT when it comes to options and capabilities. One of many extra apparent modifications is the information construction used for transferring knowledge forwards and backwards. It makes use of MessagePack, a well known open-source library for extra environment friendly binary knowledge serialization. DcRat additionally implements evasion strategies like AMSI and ETW patching, which work by disabling security measures that detect and log malicious habits – AMSI patching prevents script scanning, whereas ETW patching blocks occasion tracing. Moreover, it options an antiprocess system whereby processes whose names match these in a denylist are terminated. Blocklisted applications embrace Taskmgr.exe, ProcessHacker.exe, MsMpEng.exe, Taskkill.exe, and many others.
It’s additionally value noting that DcRat’s plugin base builds upon AsyncRAT and additional extends its performance. Among the many added plugins are capabilities equivalent to webcam entry, microphone recording, Discord token theft, and “enjoyable stuff”, a set of plugins used for joke functions like opening and shutting the CD tray, blocking keyboard and mouse enter, shifting the mouse, turning off the monitor, and many others. Notably, DcRat additionally introduces a easy ransomware plugin that makes use of the AES-256 cipher to encrypt recordsdata, with the decryption key distributed solely as soon as the plugin has been requested. Aside from that, there seem like many small modifications like a special selection of salt (a string as a substitute of a binary worth), intentionally modified variable names to additional evade detection, dynamic API decision, and plenty of extra.
VenomRAT, then again, was doubtless impressed by DcRat, as evidenced within the Figuring out variations part. The malware is full of so many options that it might be thought-about a separate menace by itself. We have now chosen to group it below AsyncRAT as their consumer elements are similar to one another. VenomRAT’s options and plugins have been documented in additional element by different distributors, so we gained’t dive deep into them on this blogpost.
Not all RATs are severe in nature although, and this is applicable equally to AsyncRAT forks. Clones like SantaRAT or BoratRAT (see Determine 4) are supposed to be jokes. Within the case of the previous, its authors have themselves acknowledged that the undertaking was principally “shamelessly ripped off of DcRat”. But, regardless of this, we’ve discovered situations of real-world utilization of them within the wild.
Determine 4. Official BoratRAT promotional emblem
Figuring out variations
Whereas doing the evaluation, we used varied strategies to establish and categorize every pattern. It must be famous that the analysis was totally on the consumer a part of the malware, as this binary is what finally ends up on victims’ machines. It comprises helpful data equivalent to malware configuration and the place details about the C&C could be discovered.
The quickest and most simple approach to establish a fork is to peek straight into the malware’s configuration, which might often be discovered within the InitializeSettings operate. The configuration values are encrypted with AES-256 and saved as base64 strings within the Settings class. Normally, the proper fork identify is available and conveniently labeled as Model. In about 90% of our analyzed samples, the Model area comprises some significant description of both the fork’s identify or the malware writer’s pseudonym. The remaining samples had this area deliberately left clean. Determine 5 illustrates the standard configuration initialization process present in DcRat and its derivatives (VenomRAT on this case).
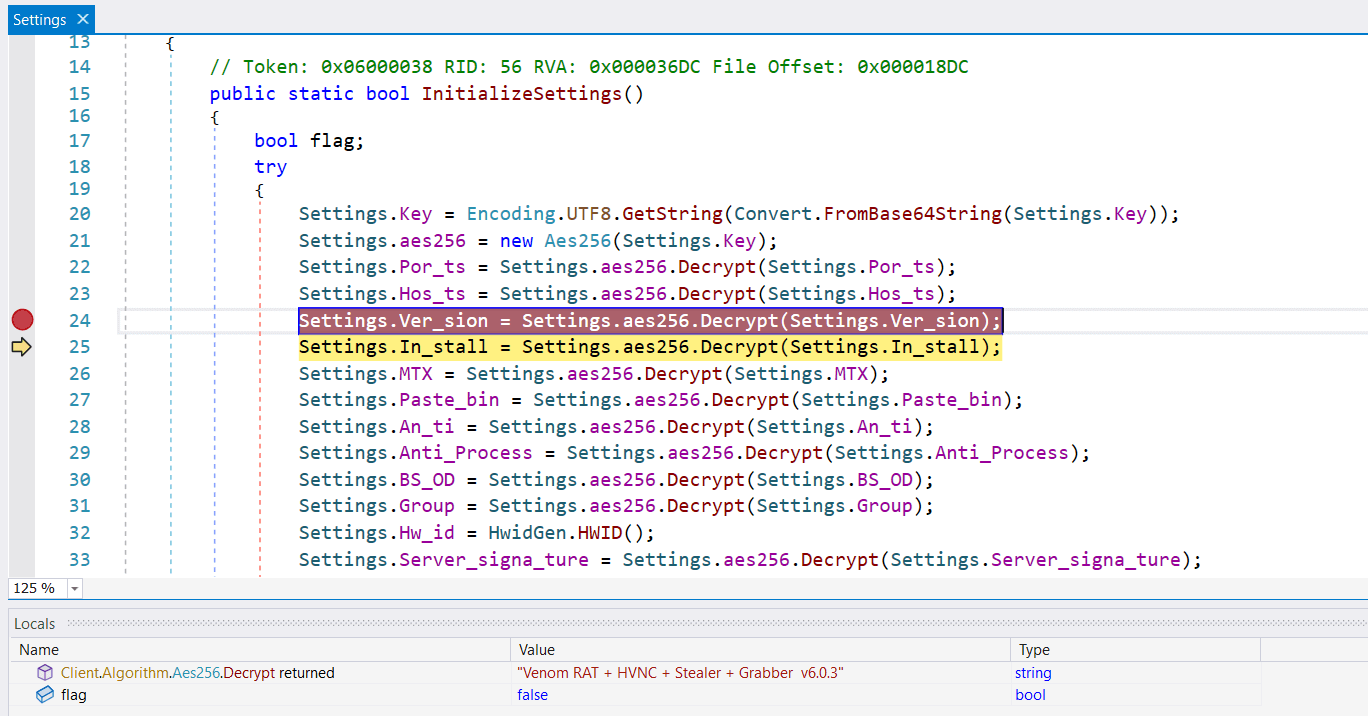
Determine 5. Initialization of VenomRAT configuration values
If the Model area is empty, generally it’s doable to get one other clue by wanting on the Salt worth used for encrypting the configuration. Attackers typically neglect this parameter when copy-pasting their very own fork. The Salt worth could be discovered within the Consumer.Algorithm.Aes256 class, as seen in Determine 6.
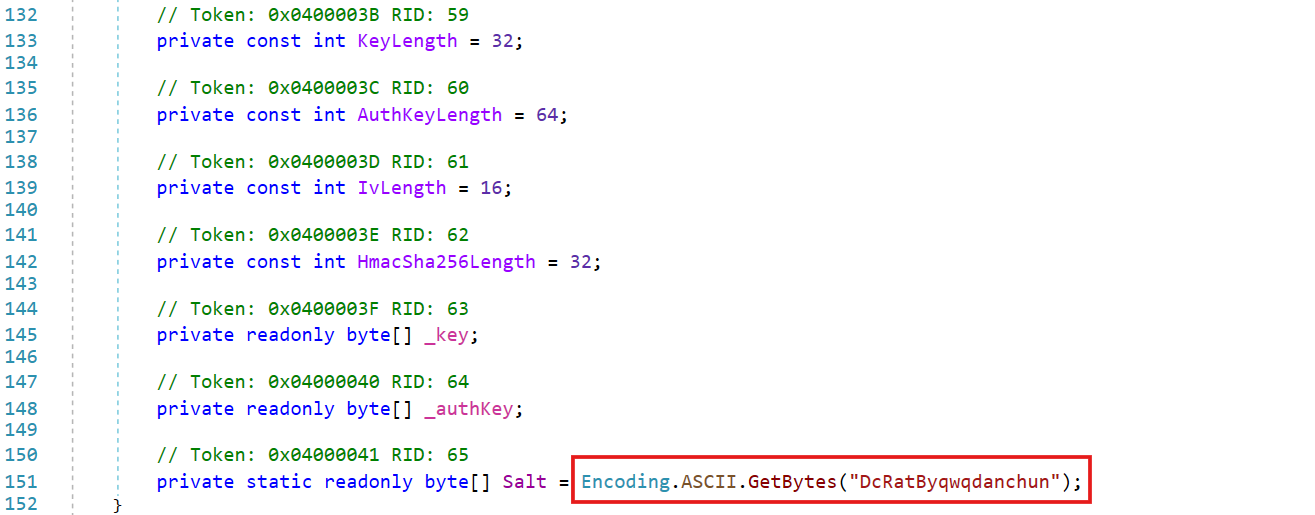
Determine 6. Extraction of the Salt worth within the constructor of VenomRAT’s cryptography class
Yet one more approach to get extra perception is to search for the embedded certificates used to authenticate the C&C server. It’s additionally situated within the configuration as a base64-encoded worth. Unpacking this worth typically reveals additional details about the server, equivalent to frequent identify, group, and organizational unit. If a selected fork has its personal identify within the Model area, it’s typically doable to hint again the earlier fork upon which it was doubtless primarily based by wanting on the CN area. Determine 7 reveals a DER-encoded certificates that reveals the BoratRAT fork, after extraction and decoding.
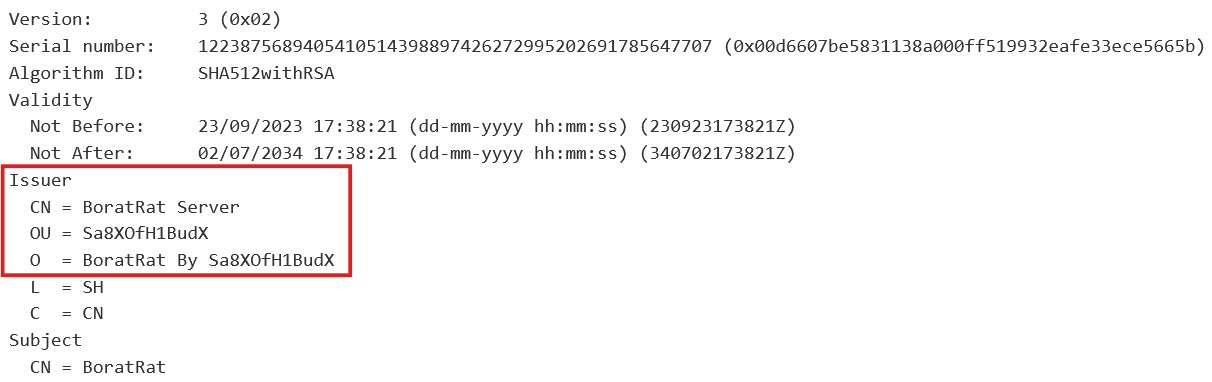
Determine 7. Consumer certificates after extraction
The strategies talked about above primarily apply to trivial instances the place malware authors both didn’t hassle to take away traces or used a default certificates. A extra subtle methodology for figuring out AsyncRAT servers exists, which includes sending a specifically crafted packet to the C&C server. This strategy is defined intimately on this Axel Mahr blogpost.
Ought to all the things else fail, figuring out the pattern origin can in the end be executed the old school means, by manually inspecting the code. This includes an in depth evaluation of the code’s construction, syntax, and performance, evaluating them towards the patterns of beforehand categorized samples.
In depth fork record
We have now highlighted right here among the extra distinguished AsyncRAT forks. As a result of sheer variety of out there forks, it isn’t possible to cowl each single one. For completeness, Determine 8 gives an prolonged record of AsyncRAT forks recognized for use for malicious functions, as seen in ESET telemetry up to now.
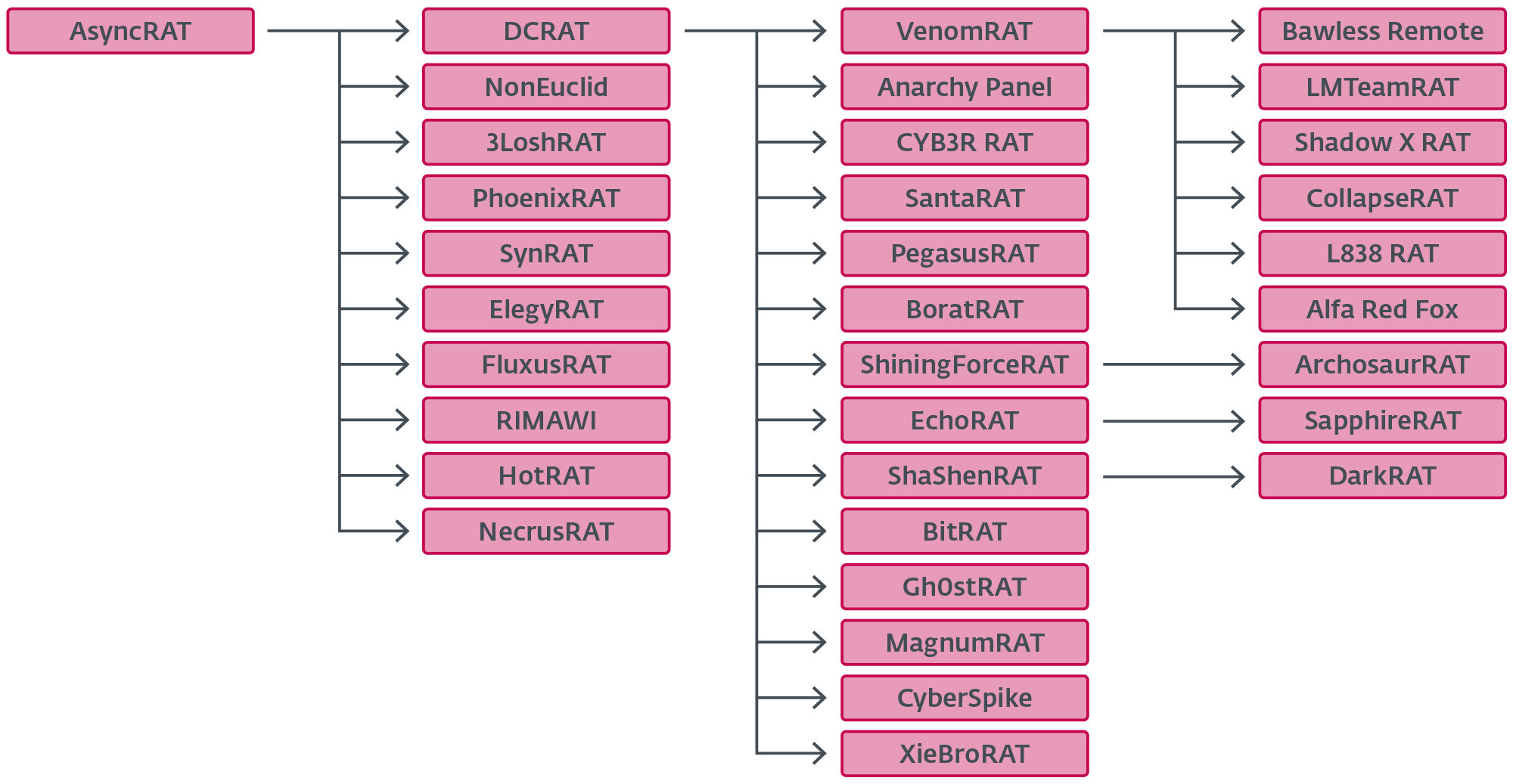
Determine 8. Prolonged fork hierarchy record
Exploring lesser-known variants
To date, we’ve talked about among the main forks that dominate the panorama. On this part, we’ve cherry-picked some lesser-known forks that improve AsyncRAT’s performance past the options included within the default variations. These unique forks are sometimes the work of 1 individual or group they usually make up lower than 1% of the quantity of AsyncRAT samples.
NonEuclid RAT
This fork stands out primarily for its inclusion of latest plugins, on high of the default ones. Whereas some plugins might sound trivial or geared in the direction of “enjoyable stuff”, others, like WormUsb.dll, have distinctly malicious functions. Desk 1 lists a choice of NonEuclid RAT plugins that deviate from the usual plugin base seen in common forks.
Desk 1. Collection of NonEuclid RAT plugins we deemed attention-grabbing
Plugin identify
Description
Screamer.dll
Bounce scare plugin.
Piano.dll
Generic audio participant.
Service.dll
Home windows companies administration.
Maps.dll
Collects geolocation data from the consumer.
WormUsb.dll
Malware spreader plugin.
Brute.dll
SSH and FTP brute forcer.
Signature Antivirus.dll
Easy signature-based file matcher.
cliper.dll
Replaces clipboard knowledge with attacker’s cryptocurrency pockets addresses.
Screamer.dll
There are 5 leap scare pictures constructed into the plugin. An attacker sends a command that signifies which picture they wish to use, together with the WAV file to be performed, and the delay after which the leap scare is triggered. Determine 9 reveals the primary three prebundled pictures an attacker might select from.



Determine 9. Three bundled leap scare pictures of the screamer plugin
Piano.dll
This plugin performs arbitrary WAV recordsdata. All sound recordsdata are saved in %appdatapercentPiano. piano.dll helps three instructions:
SetSound – provides a brand new sound file to %appdatapercentPiano,
PlayMisc – performs a requested sound file from %appdatapercentPiano, and
ClientAdd – retrieves a number of sound recordsdata from the C&C server.
Service.dll
This plugin facilitates managing Home windows companies, equivalent to beginning, stopping, and pausing companies.
Maps.dll
It is a easy plugin to gather geolocation data from the sufferer. It makes use of the .NET GeoCoordinateWatcher class to register a callback operate to gather knowledge every time the situation is offered. Among the many collected data are latitude, longitude, username, and laptop identify.
WormUsb.dll
This plugin compromises PE recordsdata with an arbitrary payload specified by the attacker.
Regardless of the time period Usb in WormUsb.dll, this plugin targets a number of places primarily based on the command supplied:
InfectExe – compromises a person PE file,
InfectExeInWindows – targets PE recordsdata in private folders (Desktop, Paperwork, Downloads, My Music), and
InfectUsbExe – targets PE recordsdata in all drives excluding the C drive.
Beneath the hood, it really works by shifting the unique file to a brief location. Then it drops a small stub instead of the unique file. This stub’s useful resource part is then populated to comprise each the unique file and the required payload, each of that are compressed and encrypted with a per-file key, generated on the time of building. Following this, the malware then obfuscates the stub by introducing proxy strategies, including customized management circulation obfuscation, and variable renaming. As a remaining contact, it embeds the unique icon and metadata within the modified stub. Determine 10 reveals the operate, with the unique methodology names, answerable for compromising a single file.
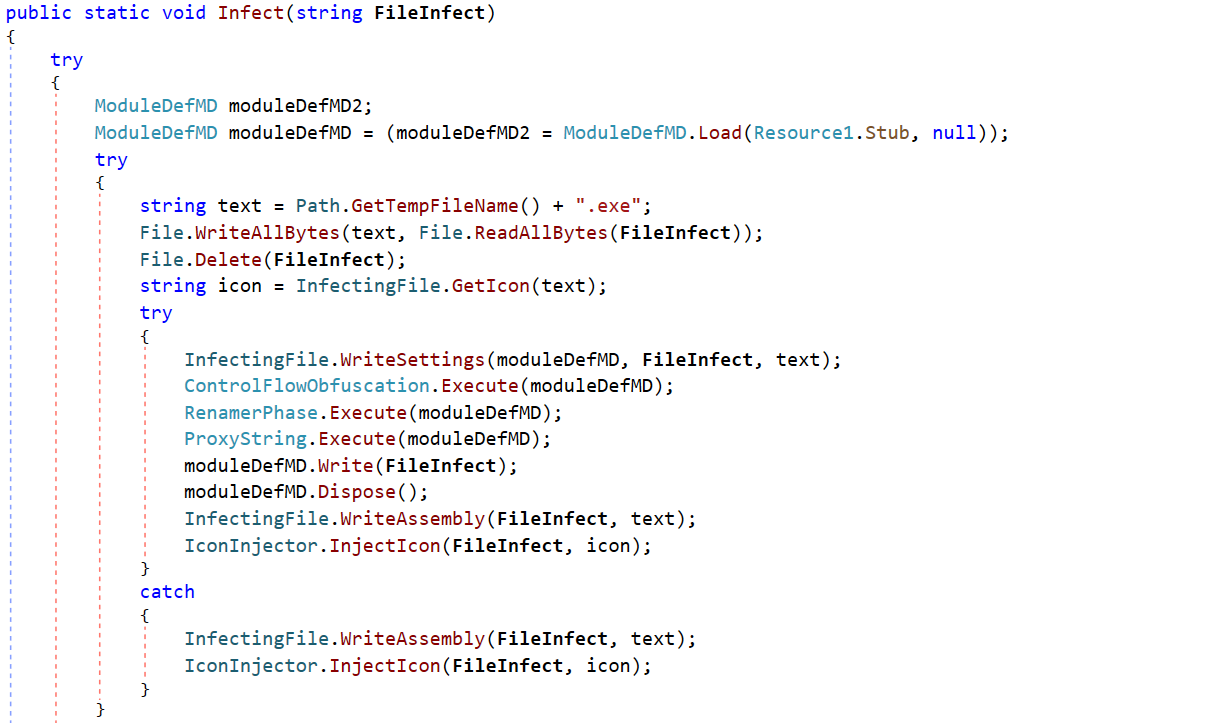
Determine 10. Compromise operate of a WormUsb.dll plugin
When such a compromised file is executed, it first decrypts, unpacks and runs the payload program, then proceeds to do the identical with the unique program.
Brute.dll
This plugin helps brute forcing of each SSH and FTP protocols from the consumer aspect. The attacker feeds it three parameters: host, login, and password, and the plugin will attempt to join utilizing these credentials. If the connection succeeds, the credentials are despatched again to the attacker with a flag indicating success. It’s not tough to think about a situation whereby an attacker may use this kind of assault to distribute brute forcing throughout a big pool of compromised machines, thus circumventing restrictions primarily based solely on the IP deal with.
Signature Antivirus.dll
The identify of the plugin implies it might need one thing to do with antivirus performance. Whereas that is technically true, it is usually a case of probably the most primitive, handbook antivirus resolution ever created. The plugin receives an inventory of MD5 hashes from the attacker and compares them to the hashes of all EXE recordsdata it finds on each disk. If an identical file is discovered, it triggers the oddly named DetectVirus operate, which merely deletes the file with none additional evaluation. This makes the identify of the plugin very doubtful at greatest. Within the fingers of the malware writer, it could have been used to delete competitor malware, or actually simply any arbitrary file.
cliper.dll
It is a standalone clipper that constantly screens the sufferer’s clipboard, and if a cryptocurrency pockets deal with is detected, it’s changed with one supplied by the attacker. Attacker-provided wallets are solely despatched when the plugin is first requested; they don’t seem to be hardcoded within the plugin. Moreover, in Determine 11, we are able to additionally see some bank card entries. This plugin comprises an intensive record of regexes that may detect each cryptocurrency wallets and bank cards, and within the case of the latter they simply get despatched again to the attacker.
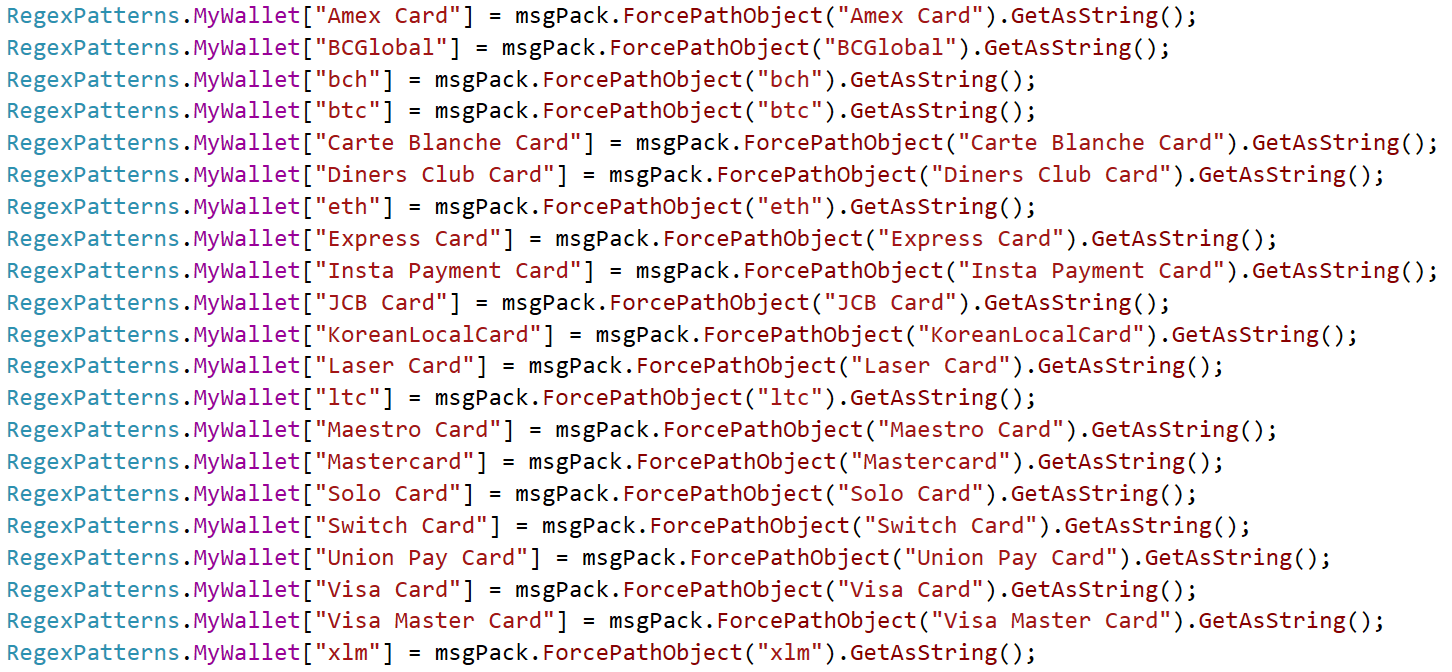
Determine 11. Wallets and playing cards monitored by cliper.dll
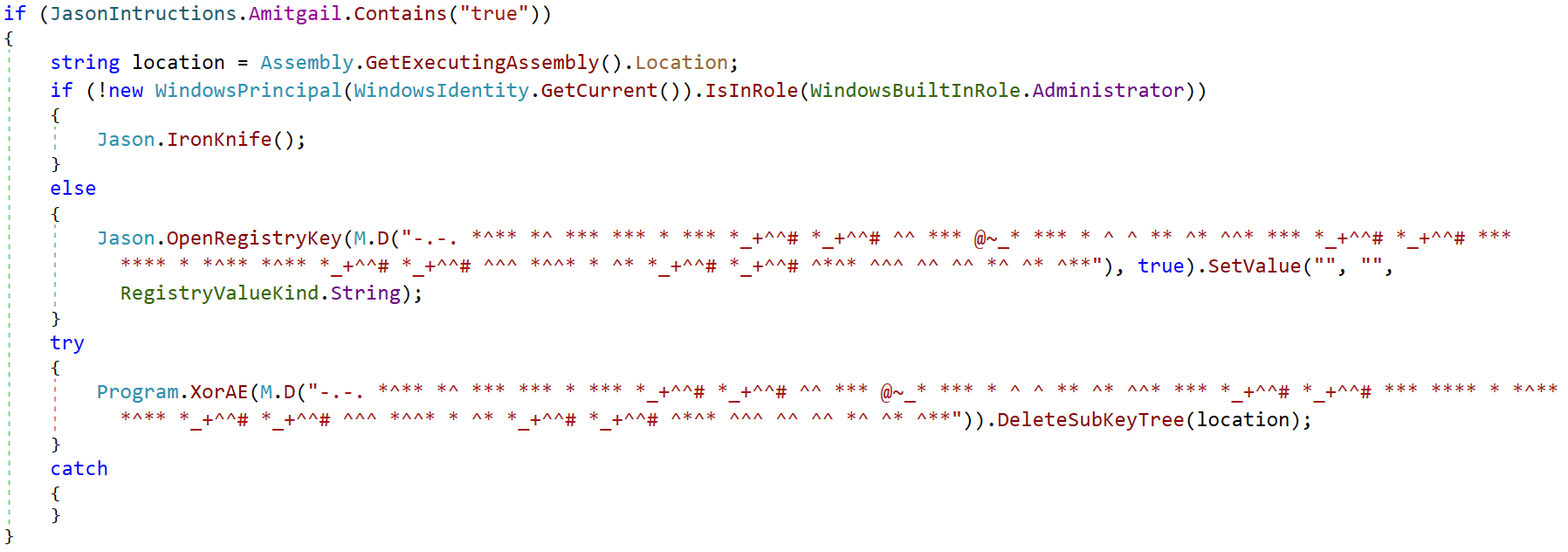
JasonRAT
Recognized in 2024, this variant reveals continued indicators of exercise. It’s attention-grabbing in that it employs obscure variable-naming conventions paying homage to “satanic” phrases from what the malware writer refers to because the Guide of Jason. In Determine 12, you possibly can see typical AsyncRAT configuration values (in base64), however with renamed variables, whereas Determine 13 reveals the logic of the principle entry level of the malware. Apart from the same old configuration values, this variant additional extends the consumer by introducing nation concentrating on.
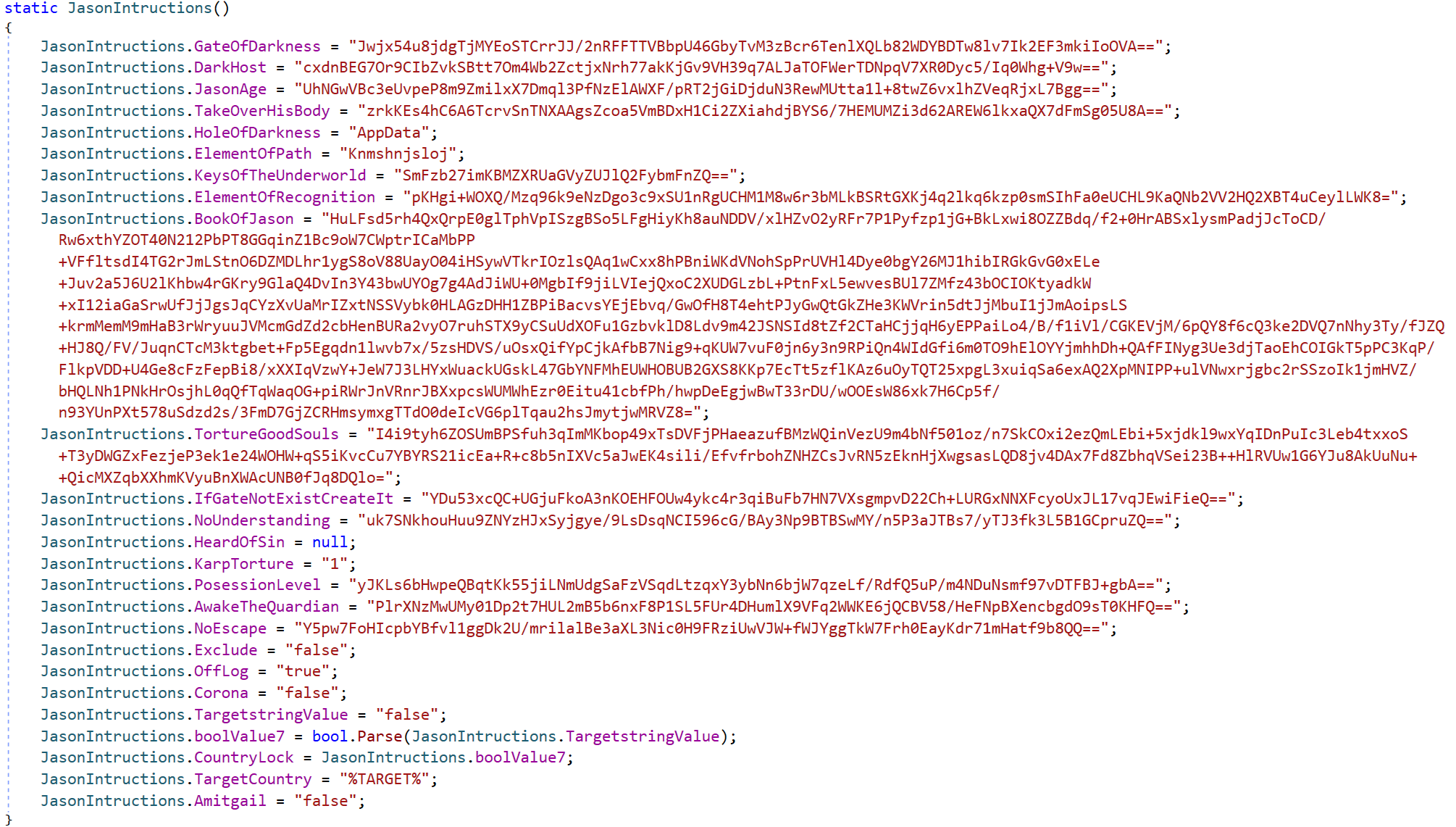
Determine 12. Partially obfuscated JasonRAT configuration values
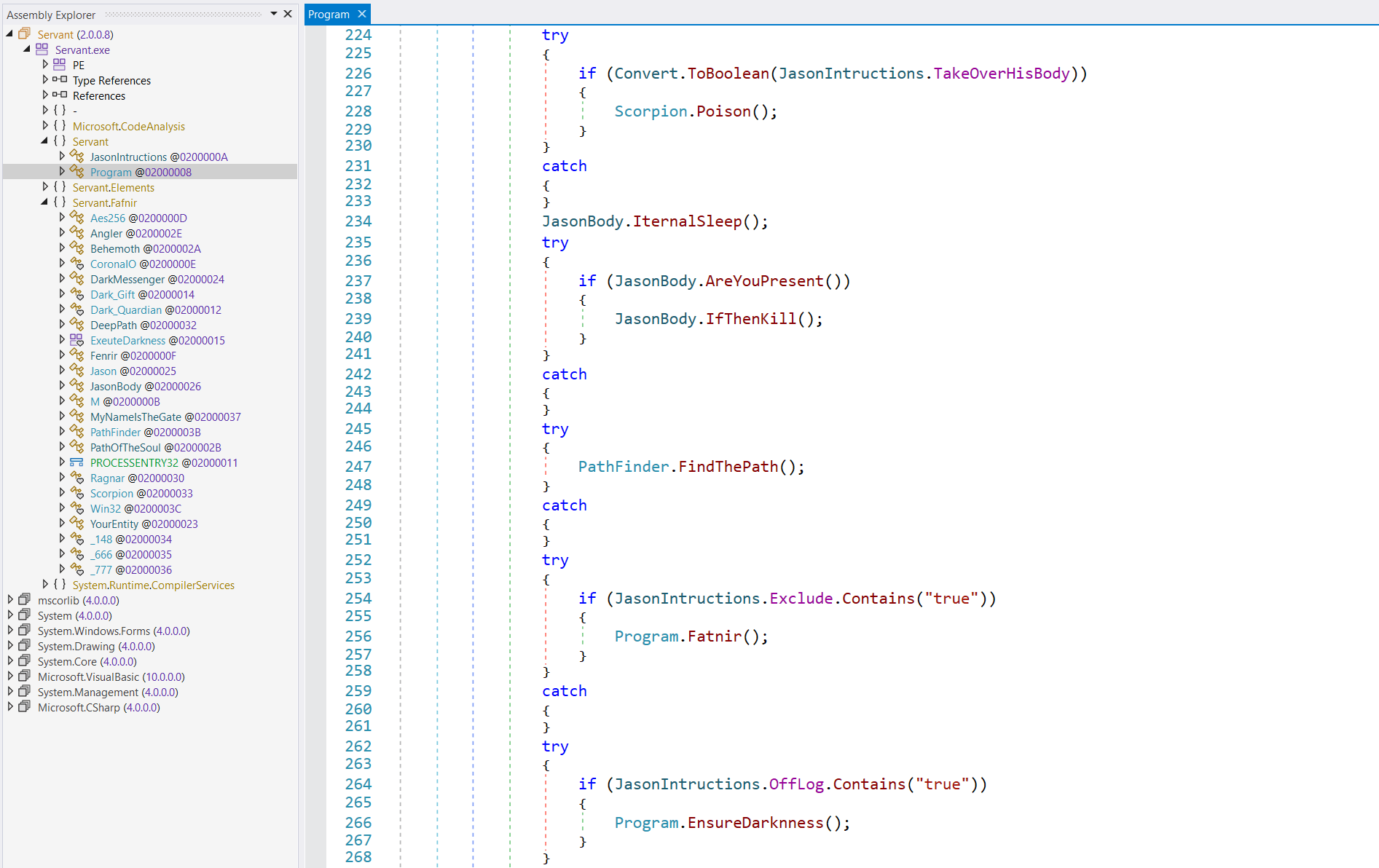
Determine 13. Most important JasonRAT entry level exhibiting renamed operate names
One other unusual function is the selection of string obfuscation. A subset of the strings employs an additional layer of obfuscation by using an prolonged variant of Morse code. Each uppercase and lowercase letters are included, in addition to some particular characters. Determine 14 reveals the encoded registry key string utilizing an prolonged mapping.
Determine 14. Prolonged Morse code used as string obfuscation in JasonRat
XieBroRAT
It is a RAT with Chinese language localization. It introduces a brand new plugin, BrowserGhost.dll, which is a browser-credential stealer. One other plugin, Abstain.dll, gives interplay with Cobalt Strike servers by making a reverse connection.
To extend the protection, the malware gives the supply chain in a number of totally different languages. The usual .NET consumer binary could be wrapped and distributed through shellcode, VBS, or JavaScript.
Lastly, the writer additional prolonged the malware by borrowing closely from open-source initiatives, integrating instruments like mimikatz, SharpWifiGrabber, SharpUnhooker, and many others.
Conclusion
AsyncRAT’s rise and its subsequent forks spotlight the inherent dangers of open-source malware frameworks. Our evaluation revealed a various and evolving ecosystem of derivatives, starting from persistent threats like DcRat and VenomRAT to lesser-known novelty forks like JasonRAT and BoratRAT, which appear to serve extra as curiosities than credible threats. All of those forks not solely prolong AsyncRAT’s technical capabilities but in addition show how shortly and creatively menace actors can adapt and repurpose open-source code.
The widespread availability of such frameworks considerably lowers the barrier to entry for aspiring cybercriminals, enabling even novices to deploy subtle malware with minimal effort. This democratization of malware improvement – particularly contemplating the rising reputation of LLMs and potential to misuse their capabilities – additional accelerates the creation and customization of malicious instruments, contributing to a quickly increasing and more and more complicated menace panorama.
In mild of those traits, it’s affordable to anticipate that future forks might incorporate extra superior obfuscation, modularity, and evasion capabilities. This potential evolution underscores the significance of proactive detection methods and deeper behavioral evaluation to successfully deal with rising threats.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis affords non-public APT intelligence studies and knowledge feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete record of indicators of compromise (IoCs) could be present in our GitHub repository.
Recordsdata
SHA-1
Filename
Detection
Description
F8E31B338123E38757F8B7099797119A038A3538
Screamer.dll
MSIL/AsyncRAT.C
NonEuclid leap scare plugin.
98223D2F8DF2F9E832AE081CD6E072A440C9A3CD
Piano.dll
MSIL/AsyncRAT.C
NonEuclid audio participant plugin.
CDEC9A1C73E3E21B1D70DDAA6BF139D8D2A197A5
Maps.dll
MSIL/AsyncRAT.C
NonEuclid geolocation plugin.
932C49EEE087D432D0DA10CC0640B11FD2C91203
Service.dll
MSIL/AsyncRAT.C
NonEuclid Home windows service administration plugin.
2FA98D088486BAC57FF60E072E28FEE5830E7B28
WormUsb.dll
MSIL/AsyncRAT.C
NonEuclid malware spreader plugin.
62C9FEFA84067F695032A6939F07C3799AAD80A3
Brute.dll
MSIL/AsyncRAT.C
NonEuclid SSH and FTP brute forcer plugin.
FAD946F7ACF017F0C50C81BF379AABA3528AFBB3
Signature Antivirus.dll
MSIL/AsyncRAT.C
NonEuclid signature-based file matcher plugin.
51B8A5818B7031EDB59A2B2ECF160A78505880BA
cliper.dll
MSIL/AsyncRAT.C
NonEuclid clipboard hijacker plugin.
4FB0CAAD6E345947EE2D30E795B711F91C6A4819
Stub.exe
MSIL/AsyncRAT.A
AsyncRAT consumer.
FD9CF01CEA7DE8631C34B988A7AAD55587A162FA
Stub.exe
MSIL/AsyncRAT.A
3LoshRAT consumer.
B8AB93E958E0DE4BE2766B2537832EDB37030429
Consumer.exe
MSIL/AsyncRAT.A
DcRat consumer.
68B58483D0E4E7CC2478D6B4FC00064ADE3D7DB3
Microsoft_Edge_Driver.exe
MSIL/AsyncRAT.A
VenomRAT consumer.
4F69E0CE283D273B724CE107DF89F11C556A7A4E
Consumer.exe
MSIL/AsyncRAT.C
BoratRAT consumer.
E4F87568473536E35006D1BD4D4C26A8809F3F91
Consumer.exe
MSIL/AsyncRAT.A
Anarchy Panel consumer.
D10B8197732437E9BF840FEA46A30EFF62892A4E
Consumer.exe
MSIL/AsyncRAT.A
CollapseRAT consumer.
0DC28EA51F0D96E0D1BC78DF829C81A84332C5F1
dwm.exe
MSIL/AsyncRAT.A
Shadow X RAT consumer.
E5B511E7550CBADE74E75EADE8F413A89D963FE5
ClientAny.exe
MSIL/AsyncRAT.A
LMTeamRAT consumer.
3124F58428184FDF75E21B1E5A58CADF9DD2BA03
Stub.exe
MSIL/AsyncRAT.A
PhoenixRAT consumer.
8402AA507CF5B1BBFAB53E3BF7A7D4500796A978
Consumer.exe
MSIL/AsyncRAT.A
EchoRAT consumer.
AB2C6F9695346FAA9495B4AB837085C1524FFDDF
Consumer.exe
MSIL/AsyncRAT.A
XieBroRAT consumer.
3E6CD9D07B8ECE706697F332AC9F32DE5ECAF086
tempClient.exe
MSIL/AsyncRAT.C
NonEuclid RAT consumer.
FF4592A8BCB58F5CF6BD70B882E886EC6906EECD
Servant.exe
MSIL/AsyncRAT.A
JasonRAT consumer.
MITRE ATT&CK strategies
This desk was constructed utilizing model 17 of the MITRE ATT&CK framework.
Tactic
ID
Identify
Description
Protection Evasion
T1562.001
Impair Defenses: Disable or Modify Instruments
DcRat terminates safety instruments equivalent to Taskmgr.exe and MsMpEng.exe.
T1562.004
Impair Defenses: Disable or Modify System Firewall
DcRat leverages AMSI and ETW bypass strategies to evade detection.
T1027.013
Obfuscated Recordsdata or Info: Encrypted/Encoded File
JasonRAT employs modified Morse code and obscure variable names to hinder evaluation.
Credential Entry
T1539
Steal Net Session Cookie
DcRat leverages a plugin to steal Discord tokens from compromised machines.
T1555.003
Credentials from Password Shops: Credentials from Net Browsers
XieBroRAT makes use of a plugin to gather browser credentials.
T1110.003
Brute Pressure: Password Spraying
NonEuclid makes use of a plugin to brute drive SSH and FTP credentials.
Discovery
T1614.001
System Location Discovery: System Language Discovery
NonEuclid makes use of a plugin that collects geolocation knowledge from compromised programs.
Assortment
T1123
Audio Seize
DcRat has a microphone plugin that allows audio seize from the sufferer’s system.
T1125
Video Seize
DcRat features a webcam plugin that permits distant entry to the sufferer’s digital camera.
T1115
Clipboard Information
NonEuclid makes use of a plugin that screens the clipboard to intercept and change cryptocurrency pockets addresses.
Impression
T1486
Information Encrypted for Impression
DcRat includes a ransomware plugin able to encrypting recordsdata on the sufferer’s system.